How I Built an AI-Assisted Log Analysis System to Catch Production Issues Before Users Did
9 min read
7 views

This AI log analysis system was built to solve a growing production issue detection gap. Despite having structured logs and monitoring, critical signals were lost in noise, limiting effective AI log monitoring. As systems scaled, manual log analysis failed, making log analysis automation essential. This shift enabled proactive incident detection instead of reactive debugging.
For a long time, our production setup looked “correct” on paper. Structured logs, centralized logging, alerts based on error rates, and dashboards for latency. Yet incidents still reached users before engineers noticed.
The problem wasn’t missing data. It was human attention.
As traffic grew, logs became noise. Important signals were buried under repetitive entries, retries, and edge cases. Engineers reacted instead of anticipating. That’s when I realized logging systems are passive by default. They wait for humans to ask the right questions.
AI changes that dynamic.
The Core Shift – From Searching Logs to Letting Logs Explain Themselves
Traditional log analysis assumes engineers know what to look for. In reality, most production issues are novel combinations of known events. The signal is not a single error line. It’s a pattern across time, services, and context.
The goal wasn’t to “add AI” for the sake of it. The goal was to let the system surface unusual behavior automatically.
That reframed the problem as pattern detection, not keyword search.
Where AI Fits (and Where It Shouldn’t)
I didn’t replace the logging stack. That would have been reckless. Instead, I layered AI on top of what already worked.
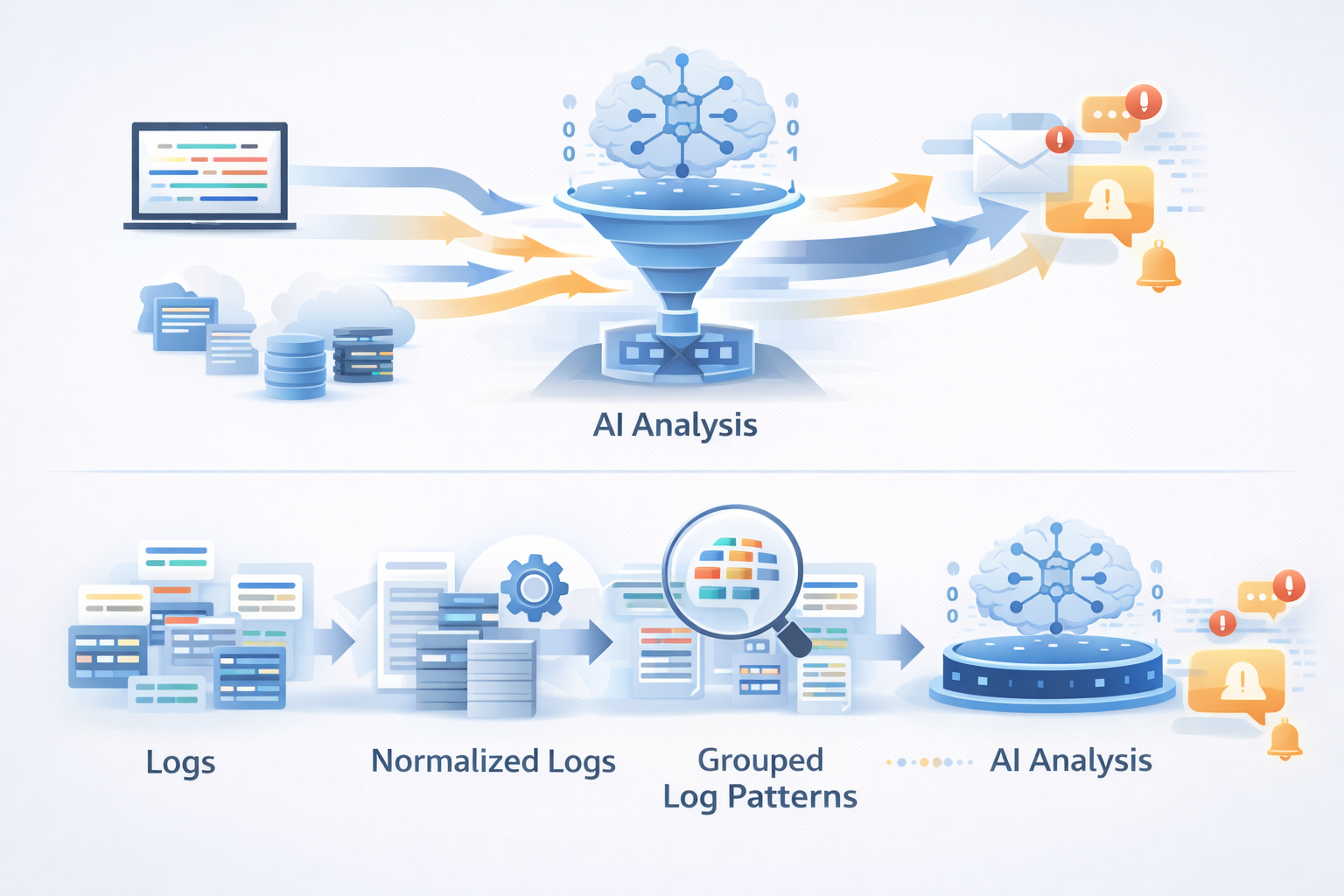
The flow looked like this:
Logs were still collected normally. They were parsed, structured, and stored the same way. A secondary pipeline periodically sampled recent logs, grouped them by service and endpoint, and summarized them into compact text blocks.
Only these summaries were sent to the AI layer.
This mattered for two reasons. Cost stayed predictable, and sensitive raw data never left the system.
Preparing Logs for AI Without Overengineering
Raw logs are terrible AI input. They are repetitive and verbose. The first step was normalization.
At ingestion time, logs were already structured as JSON. Before analysis, I collapsed similar messages into templates. Dynamic values like IDs and timestamps were abstracted so the AI could focus on behavior, not noise.
A simplified example of this transformation looked like this:
function normalizeLog(log) {
return log.message
.replace(/\d+/g, "<num>")
.replace(/[a-f0-9-]{36}/g, "<uuid>");
}This wasn’t about perfection. It was about consistency.
Letting AI Detect What Humans Miss
Once logs were normalized and grouped, the AI’s job was simple: compare recent patterns with historical ones and explain what looked different.
The prompt was deliberately constrained. Instead of asking vague questions, I asked:
“Given these summaries, what patterns look new, abnormal, or risky compared to typical behavior?”
This framing mattered. It prevented generic answers and forced comparison-based reasoning. The AI didn’t replace alerts. It augmented them by answering why something might matter.
A Real Example That Justified the Entire System
One night, error rates stayed within thresholds. No alerts fired. The AI summary flagged something subtle.
A background job started retrying more often, but still succeeded eventually. Latency increased only slightly. No alarms.
The AI flagged a new retry pattern correlated with a recent deploy. We rolled back proactively. The next day, we discovered the issue would have caused a cascading failure under peak load.
That single catch justified the system.
Why This Wasn’t Real-Time
It’s tempting to push AI into real-time alerting. I chose not to.
Real-time systems demand deterministic behavior. AI is probabilistic. Mixing the two creates alert fatigue fast.
Instead, this system ran on intervals. It acted like a second brain doing quiet analysis in the background. Engineers reviewed summaries during standups or incident reviews. That balance preserved trust.
Tradeoffs I Accepted Intentionally
This system does not catch everything instantly. It trades immediacy for insight.
There is also cost involved. Even with summaries, AI usage isn’t free. That’s why sampling and scope control are critical.
The upside is leverage. One engineer can reason about patterns across millions of log lines without staring at dashboards all day.
How This Changed Engineering Behavior
The most interesting outcome wasn’t technical. It was cultural.
Engineers stopped reacting only to alerts. They started asking better questions. Deploy reviews included AI summaries. Postmortems became clearer because anomaly explanations were already written.
Logs stopped being an archive. They became a narrative.
Final Takeaway
AI doesn’t replace observability. It restores its usefulness.
When systems grow beyond what humans can mentally simulate, the job of tooling is not to show more data. It’s to explain what changed.
Used carefully, AI becomes a multiplier for engineering judgment, not a crutch.
Suggested Links
If you’re interested in how backend systems quietly degrade before anyone notices, this AI-driven log analysis connects closely with a previous breakdown where a single missing database index caused response times to spike from milliseconds to seconds. Both issues share the same root problem: signals were present, but invisible until someone looked the right way.
This also pairs naturally with the Redis cache invalidation case study, where performance issues were behavioral rather than obvious failures. AI-based pattern detection helps surface these subtle inconsistencies earlier, before they become user-facing incidents.
Frequently Asked Questions
If you're building something complex and want a second brain before things get expensive — let's talk.
Continue Reading

Backend Engineering17 min read
How a Hidden N+1 Query Slowed API by 6x and the Exact Steps I Used to Fix It
The API wasn’t crashing. Nothing looked broken. But production response times quietly became six times slower. This is a real-world breakdown of how a hidden N+1 query slipped through reviews, how I proved it in Laravel, and the exact steps that fixed it permanently.
Mar 12, 2026131 views

Backend Engineering14 min read
Why OFFSET Pagination Broke Our API at Scale (And How Cursor Pagination Fixed It)
OFFSET pagination broke our API at scale, causing slow queries and latency spikes. Learn how cursor pagination fixed performance without breaking clients.
Jan 16, 20265 views

Backend Engineering15 min read
Our Cache Made the App Slower. The Redis Cache Mistake I’ll Never Repeat
We added caching to speed things up. Latency dropped, then quietly got worse. This is a real production bug breakdown of how a Redis cache invalidation mistake slowed critical pages and how I fixed it without rewriting the backend.
Jan 15, 20263 views